Configuration Reference
With DiscrimiNAT, the Firewall Rules attached to the applications that need filtered access to the Internet can be annotated with the set of allowed FQDNs. This allows creating least privilege egress policies from the protected workload to the Internet.
No need to create VPC-wide allowlists that allow discrete applications access to what they needn't.
DiscrimiNAT's own Firewall Rules need not be altered.
On this page, we cover the syntax for the Cloud-native Firewall Rules' description fields, where the annotations live.
See-Thru mode
The see-thru mode is a non-blocking configuration that allows one to build an appropriate allowlist 🎥 up to a specified date. The annotation is added to the description fields of egress rules of protected applications to-be.
Syntax
discriminat:see-thru:YYYY-mm-dd
The rule will automatically stop working after the YYYY-mm-dd date.
Examples
discriminat:see-thru:2025-12-31
discriminat:see-thru:2025-09-09
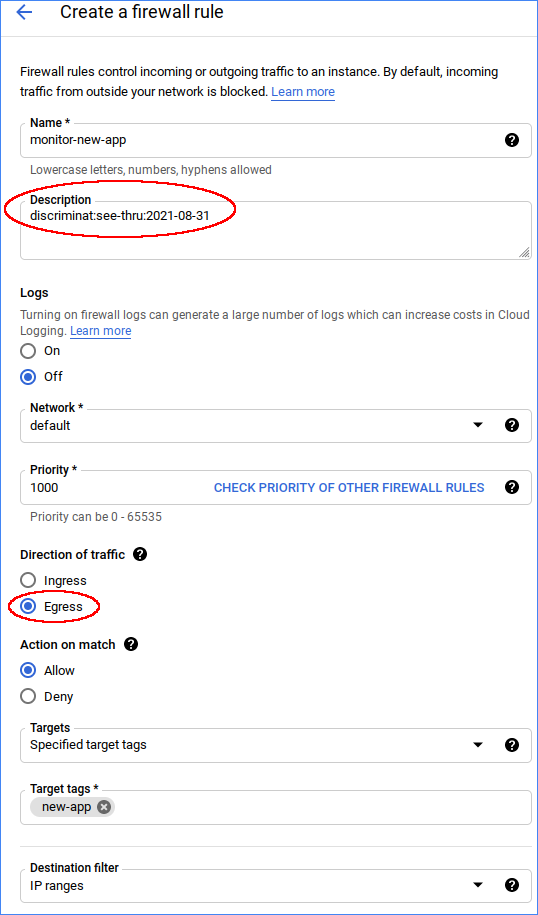
Configuring this mode in the GCP web console would look like:
In Terraform, this would be along the lines of:
resource "google_compute_firewall" "some-app" {
name = "monitor-some-app"
network = var.network
direction = "EGRESS"
destination_ranges = ["0.0.0.0/0"]
allow {
protocol = "all"
}
target_tags = ["new-app"]
description = "discriminat:see-thru:2025-12-31"
}
Logs
The flow logs at logName="projects/<google-cloud project name>/logs/discriminat-flow" in Logs Explorer will have three additional fields for traffic from any workload that has a Firewall Rule with a see-thru annotation in it:
see_thru_exerted: true when notlsorsshprotocol rules allowed this connection through and it's only because of thesee-thrurule that the connection has been let through. false when an already presenttlsorsshprotocol rule would otherwise allow this connection through. The rest of the fields in the log line remain as they would without thesee-thrurule, hence indicating whichtlsorsshprotocol rule matched to let this connection through.see_thru_gid: The Firewall Rule where the enactedsee-thruwas found.see_thru_days_remaining: The number of remaining days this rule will continue to work. Runs into negative if the current date goes past the specified date. These log fields are still emitted if asee-thrurule with any date, past or future, remains specified.
TLS and SSH mode
The tls and ssh modes are a blocking configuration that will only allow FQDNs set out in the allowlist. Destination protocols, FQDNs and IP Addresses are added to the description fields of egress rules of the protected applications.
If transitioning from a see-thru rule, note that tls and ssh rules require a specific port number to be specified in the Firewall Rules.
Syntax
discriminat:<protocol>:<Secret Path> (Secret Path variant)
discriminat:<protocol>:<fqdn>[,<fqdn>,<ipv4>] (Inline variant)
- Valid protocols are
sshandtlsonly. - There can be other text leading and trailing this specification, separated by whitespace.
- All of it is case insensitive, except the Secret Path if specified.
- Wildcards are only supported for the TLS protocol.
Please familiarise yourself with operation and caveats on the behaviour of wildcard rules before using them.
Secret Path variant
- The <Secret Path> is the full path of a Secret. It can be in another GCP Project as well, as long as DiscrimiNAT's Service Account has Secret Manager Secret Accessor Role to read it.
- If using our Terraform modules, see the Terraform section on the Service Account page for example code.
- The JSON format for list of FQDNs and IP Addresses in the payload of a Secret is:
{
"addrs": [
"fqdn1.com",
"*.github.com",
"203.0.113.9",
...
]
}
Examples
If the above payload were to be stored in a Secret called service-foo-allowed-fqdns, its full path could be projects/000000000000/secrets/service-foo-allowed-fqdns. Therefore, what goes in description field will be:
discriminat:tls:projects/000000000000/secrets/service-foo-allowed-fqdns
Configuring this variant in the GCP web console would look like:

Common constraints to both variants
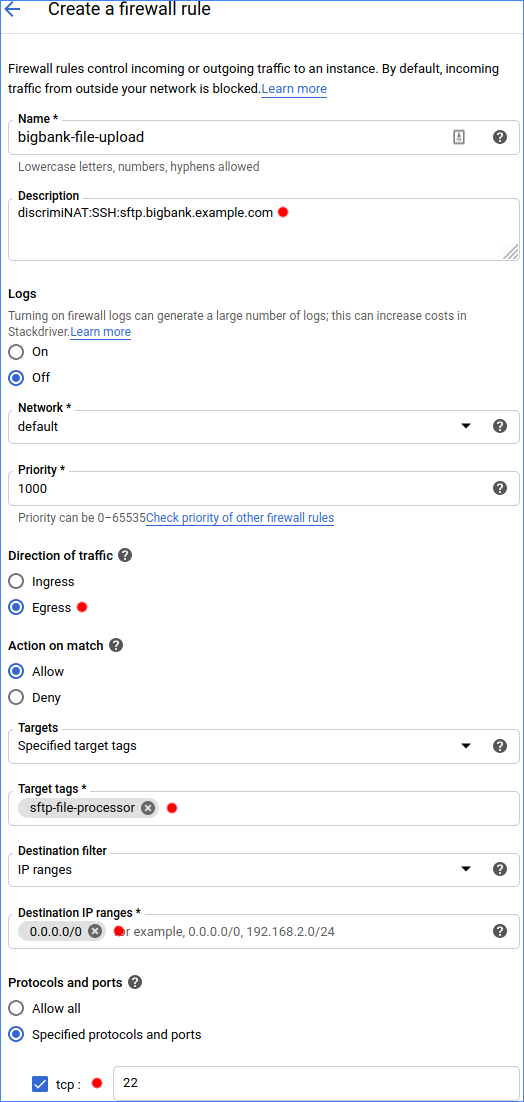
Direction of trafficmust beEgress.Targetsmust be set toSpecified target tags. And then specify the same Network Tags as on the virtual machines that you'd like this firewall rule to be applied to. Precisely like you would anyway.- Under
Protocols and ports, only choosetcpand specify exactly one port number. To use another port for an alternative set of addresses, simply create another Firewall Rule with that port number. See the Connecting to MS/Azure SQL Server over TLS guide for an example. - For your typical HTTPS outbound connection, the port number would be
443. - A typical SFTP connection has the port number of
22. - Kafka typically, as another example, is on port
9092. Destination filtermust be set toIP rangeand the range set to the narrowest you can think of. Now if you don't have anything narrower than0.0.0.0/0that is absolutely fine! The firewall takes care of validating the destination IP address of actual packets in many ways, but the Firewall Rule at the Google Cloud networking and security level must allow the packet to leave the virtual machine at all.0.0.0.0/0is a safe choice with the DiscrimiNAT Firewall in the way.- Multiple Firewall Rules can be associated with the virtual machines with the use of Network Tags, and they will all be recognised.
Inline variant
- There can be as many FQDNs and IP Addresses as you can fit separated by commas. There cannot be whitespace, though.
- Multiple Firewall Rules can be created to accommodate more addresses, or group them by some criteria.
Examples
DiscrimiNAT:TLS:api.foo.example.com,downloads.example.net,203.0.113.9DiscrimiNAT:SSH:sftp.txs.example.org,ssh.github.comdiscriminat:tls:api-v?.example.com discriminat:tls:www.example.orglorem ipsum discriminat:ssh:ssh.github.com,gitlab.com,203.0.113.9 dolor sit amet
Configuring this variant in the GCP web console would look like:
In Terraform, this would be along the lines of:
resource "google_compute_firewall" "acme" {
name = "acme-reports-upload"
network = var.network
direction = "EGRESS"
destination_ranges = ["0.0.0.0/0"]
allow {
protocol = "tcp"
ports = ["443"]
}
target_tags = ["acme"]
description = "discriminat:tls:api.acme.com,auth.acme.com,203.0.113.9,foo.example.com,bar.example.net"
}
Complete Bypass
If you would like to discuss alternate protocols or know how to completely bypass the DiscrimiNAT whilst still routing traffic, get in touch with our DevSecOps Support to discuss the best option for your use case.